Phishing prevention has become essential as more criminals turn towards online scams to steal your personal information. We’ve learned to dodge spam emails, but phishing emails can look deceivingly credible. Some are even personalized specifically for you. Since you will likely be exposed to a phishing attack eventually, you’ll need to know the red flags. Because scams are nothing new on the web, but phishing is harder to spot than you might think.
Across the web, phishing attacks have baited unsuspecting victims into handing over bank info, social security numbers, and more. Plus, cybercriminals have become even savvier with their disguises. Clicking a link within an email may make you a victim of a scam.
As we dive into how to prevent phishing, we’ll answer some important questions:
- What is phishing?
- Am I at risk of being a phishing target?
- What types of phishing scams exist?
- How do I spot a phishing scam?
- What is phishing email?
- What do I do once I’ve identified a phishing email?
- What should I do to avoid being a victim of phishing?
What is Phishing?
Phishing persuades you to take an action which gives a scammer access to your device, accounts, or personal information. By pretending to be a person or organization you trust, they can more easily infect you with malware or steal your credit card information.
In other words, these social engineering schemes “bait” you with trust to get your valuable information. This could be anything from a social media login, to your entire identity via your social security number.
These schemes may urge you to open an attachment, follow a link, fill out a form, or reply with personal info. By that logic, you must be on guard at all times.
The most common scenario is as follows:
- You open your email and suddenly an alert from your bank appears in your inbox. When you click the link in the email, you are taken to a webpage that looks, more or less, like your bank. These are known as scam or fraudulent websites that are created with the intention of tricking visitors into providing your login credentials or financial information, or to sell illegitimate or non-existent products or services.
- After entering your credentials on the page that appears, you are usually sent to the actual institution to enter your information a second time. By steering you to the legitimate institution, you don't immediately realize your information was stolen.
These threats can get very elaborate and show all types of communication, even phone calls. The danger of phishing is that it can deceive anyone that isn’t skeptical of smaller details.
To help you guard yourself without becoming paranoid, let’s unpack how phishing attacks work.
How does Phishing work?
Anyone who uses the internet or phones can be a target for phishing scammers.
Phishing scams normally try to:
- Infect your device with malware
- Steal your private credentials to get your money or identity
- Obtain control of your online accounts
- Convince you to willingly send money or valuables
Sometimes these threats don’t stop with just you. If a scammer gets into your email, contact list, or social media, they can spam people you know with phishing messages seemingly from you.
Trust and urgency are what makes phishing so deceiving and dangerous. The perpetrator of a phishing attack seeks to create a sense of urgency. If they can gain your confidence and trust, they can convince you to take desired action before thinking things through. It's important to be familiar with the traits of a phishing attempt in order to protect yourself from falling victim to them.
Who is at risk of Phishing attacks?
Phishing can affect anyone of any age, whether in their personal life or in the workplace.
Anyone from the elderly to young children are using internet devices nowadays. If a scammer can find your contact information publicly, they can add it to their phishing target list.
Your phone number, email address, online messaging IDs, and social media accounts are harder to hide nowadays. So, there’s a good chance that just having one of these makes you a target. Plus, phishing attacks can be broad or highly targeted in the people they choose to trick.
Spam Phishing
Spam phishing is a broad net being thrown to catch any unsuspecting person. Most phishing attacks fall into this category.
To explain, spam is the electronic equivalent of the ‘junk mail’ that arrives on your doormat or in your postbox. However, spam is more than just annoying. It can be dangerous, especially if it’s part of a phishing scam.
Phishing spam messages are sent out in mass quantities by spammers and cybercriminals that are looking to do one or more of the following:
- Make money from the small percentage of recipients that respond to the message.
- Run phishing scams – in order to obtain passwords, credit card numbers, bank account details and more.
- Spread malicious code onto recipients’ computers.
Spam phishing is one of the more popular means that scammers get your info. However, some attacks are more targeted than others.
Targeted Phishing
Targeted phishing attacks usually refers to spear phishing or its most common variant, whaling.
Whaling takes on high-level targets, while spear phishing widens the net. Targets usually are employees of specific companies or government organizations. However, these scams can easily be aimed at anyone seen as particularly valuable or vulnerable.
You might be targeted as a customer of a targeted bank, or an employee of a healthcare facility. Even if you’re just responsive to a strange social media friend request, you might be phished.
Phishers are much more patient with these schemes. These personalized scams take time to craft, either potentially for a reward or to increase the chances of success.
Building these attacks may involve gathering details about you or an organization you happen to be involved with.
Phishers might take this information from:
- Social media profiles
- Existing data breaches
- Other publicly discoverable info
Moving in for an actual attack might be swift with an immediate attempt to encourage you to take action. Others might build a connection with you for months to earn your trust before the big “ask.”
These attacks aren’t limited to direct messages or calls — legitimate websites might be hacked directly for a phisher’s benefit. If you’re not careful, you might be phished just by logging in to site that is normally perfectly safe.
Unfortunately, it seems many people are convenient targets for these criminals. Phishing has become a new “normal” as these attacks have ramped up in frequency.
What types of Phishing Scams should I know about?
The first hurdle is understanding what to expect from phishing. It can be delivered in all kinds of means, including phone calls, texts, and even in hijacked URLs on perfectly legitimate websites.
Phishing is much easier to understand once you’ve seen it in action. You’ve probably already seen a few of these scams and just chucked them aside as spam.
Regardless of how they are targeted, phishing attacks take many roads to get to you and most people are likely to experience at least one of these forms of phishing:
- Phishing email appears in your email inbox — usually with a request to follow a link, send a payment, reply with private info, or open an attachment. The sender’s email might be tailored to closely resemble a valid one and may contain info that feels personal to you.
- Domain spoofing is a popular way an email phisher might mimic valid email addresses. These scams take a real company’s domain (ex: @america.com) and modify it. You might engage with an address like “@arneria.com” and fall victim to the scheme.
- Voice phishing (vishing) scammers call you and impersonate a valid person or company to deceive you. They might redirect you from an automated message and mask their phone number. Vishers will try to keep you on the phone and urge you to take action.
- SMS phishing (smishing) similarly to vishing, this scheme will imitate a valid organization, using urgency in a short text message to fool you. In the message, you’ll usually find a link or a phone number they want you to use. Mobile messaging services are also at risk of this.
- Social media phishing involves criminals using posts or direct messages to persuade you into a trap. Some are blatant like free giveaways or sketchy “official” organization pages with an urgent request. Others might impersonate your friends or build a relationship with you long-term before ‘attacking’ to seal the deal.
- Clone phishing duplicates a real message that was sent previously, with legitimate attachments and links replaced with malicious ones. This appears in email but may also show up in other means like fake social media accounts and text messages.
In other cases, legitimate websites might be manipulated or imitated via:
- Watering hole phishing targets popular sites that many people visit. An attack like this might try to exploit weaknesses in a site for any number of other phishing attacks. Delivering malware, link redirection, and other means are common in these schemes.
- Pharming (DNS cache poisoning) uses malware or an onsite vulnerability to reroute traffic from safe websites to phishing sites. Manually typing a URL will still lead visitors to the malicious site if it is a victim of pharming.
- Typosquatting (URL hijacking) tries to catch people who type an incorrect website URL. For example, a website might be created that is one letter off from a valid one. Typing “wallmart” instead of “walmart” could potentially lead you to a malicious site.
- Clickjacking uses a website’s vulnerabilities to insert hidden capture boxes. These will grab user login credentials and anything else you might enter on the otherwise safe site.
- Tabnabbing happens when an unattended fraudulent page reloads into an imitation of a valid site login. When you return to it, you might believe it to be real and unknowingly hand over access to your account.
- HTTPS phishing gives a malicious website the illusion of security with the classic “padlock next to the URL bar” indicator. While this encryption sign used to be exclusive to sites that were verified as safe, now any site can get this. So, your connection and info you send may be blocked to outsiders, but you’re already connected to a criminal.
Even your actual internet connection can be compromised by:
- Evil twin attacks mimic official public Wi-Fi at locations like coffee shops and airports. This is done in efforts to get you to connect and eavesdrop on all your online activity.
Finally, here are some more types of phishing you should be aware of:
- Search engine results phishing uses methods to get a fraudulent webpage to appear in search results before a legitimate one. It is also known as SEO phishing or SEM phishing. If you don’t look carefully, you may click the malicious page instead of the real one.
- Angler phishing impersonates a customer service representative for a real company to trick you out of information. On social media, a fake help account spots your “@mentions” to company’s social handle to respond with a fake support message.
- BEC (business email compromise) involves various means of breaching a company’s communications circle to get high-value info. This can include CEO impersonation or pretending a vendor with a fake invoice to initiate activities like wire transfers.
- Cryptocurrency phishing targets those with cryptocurrency wallets. Instead of using long-term means to mine cryptocurrency themselves, these criminals try to steal from those that already have these funds.
The truth is the list of types of phishing attacks is extensive and constantly expanding. These are some of the most common currently, but you might see new ones even in a few months.
Since these scams rapidly change to fit current events, they’ve been hard to spot. But there are ways you can keep yourself safer and being aware of the latest scams is an easy way to start.
Some examples of common phishing scams
Whilst it would be impractical and impossible to list every known phishing scam here, there are some more common ones you should definitely look out for:
Iran Cyberattack phishing scams use an illegitimate Microsoft email, prompting a login to restore your data in attempts to steal your Microsoft credentials. Scammers use your fear of being locked out of Windows and the relevance of a current news story to make it believable.
Office 365 deletion alerts are yet another Microsoft-related scam used to get your credentials. This email scam claims that a high volume of files have been deleted from your account. They give a link for you to login, of course resulting in your account being compromised.
Notice from bank. This scam tricks you with a fake account notification. These emails normally give you a convenient link which leads to a web form, asking for your bank details “for verification purposes.” Do not give them your details. Instead, give your bank a call as they may want to take action on the malicious email.
Email from a ‘friend’. This scam takes the form of a known friend who is in a foreign country and needs your help. This ‘help’ normally involves sending money to them. So, before you send your ‘friend’ money, give them a call first to verify whether it’s true or not.
Contest winner/Inheritance email. If you’ve won something unexpectedly or received an inheritance from a relative you've never heard of — don’t get too excited. Because, most of the time these emails are scams that require you click on a link to enter your info for prize shipment or inheritance ‘verification’.
The tax refund/rebate. This is a popular phishing scam as many people have annual taxes which they pay or have to submit payment to. These phishing messages normally say that you are either eligible to receive a tax refund, or you have been selected to be audited. It then requests that you submit a tax refund request or tax form (asking for your full details), which scammers then use to either steal your money and/or sell your data on.
Coronavirus phishing scams and malware threats
Coronavirus/COVID-19 phishing scams are the latest to weaponize fear for cybertheft. One of the most notable is the Ginp banking trojan which infects your device and opens a web page with a “coronavirus finder” offer. It baits people into paying to learn who is infected nearby. This scam ends with criminals taking off with your credit card info.
There have also been cases of scammers pretending to be important government bodies and even the World Health Organization (WHO). This scam involves scammers contacting users directly, usually by email. Requesting bank details or asking you to click on a link — in an attempt to infect your computer with malware and steal your private data.
These emails and messages may look official, but if you investigate the link URL (by hovering over the link, again, do not click it) or the email address carefully, there are usually tell-tale signs that they are not authentic and should not to be trusted (such as WHO or government emails coming from a Gmail account, etc.).
Do not fall for these scams. These organizations will never ask you for sensitive personal details or private banking details. And, the chances of them asking you to download an app or software onto your computer is also incredibly low. So, if you receive an email or message like this, especially out of the blue, do not click on the links and do not give them your personal information or bank details. Check with the applicable authorities or your bank if you’re unsure, and only use/visit trusted websites and sources.
If you receive one of these emails, this is what you should do:
1. Verify the sender by checking their email address — WHO sender addresses use the person@who.int pattern. NOT Gmail, etc.
2. Check the link, before you click — make sure the links start with https:// and not http://
3. Be careful when providing personal information — never provide your credentials to third parties, not even the WHO.
4. Do not rush or panic react — scammers use this in order to pressure you into clicking links or opening attachments.
5. If you gave sensitive information, don’t panic — reset your credentials on sites you've used them. Change your passwords and contact your bank immediately.
6. Report all scams — Go to https://www.who.int/about/contact-us
Primarily, phishing emails are laced with similar traits that a trained eye should be able to catch. However, these aren’t always easy to spot at first glance, so let’s unravel these red flags.
Phishing email example: Two-factor authentication scam
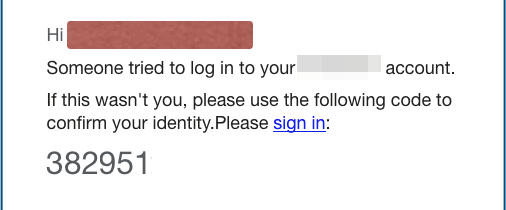
Two-factor authentication, or 2FA, is one of the best ways to protect your personal or financial information. When you log onto a site — say your online bank or credit card provider — you’ll have to provide your username and password as usual. If you have two-factor authentication enabled, the site will then send a text or email to you with a code. You must enter that code before you can complete your log in to the site.
Scammers, though, are now using this extra security measure as a way to trick you. A phishing campaign is out there targeting social media users, sending them emails claiming that someone has tried to log into their accounts.
The email asks recipients to sign into a site that is supposedly run by a social media service. In this case, this is an illegitimate site. But what’s interesting is that the scammers include a code at the bottom of the message, implying that users should type that code in — as if it was an example of two-factor authentication — when they sign into the spoofed web page.
How can you tell it’s fake?
This is a well-done scam. There is one tell-tale sign that the email is fake, though. If you click on the link and access the spoofed website, the domain name displayed in your browser’s address bar will most likely not be from the official social media website. That’s why it’s smart not to click. Instead, hover over the link to see the true address.
Phishing email example: Tax refund scam
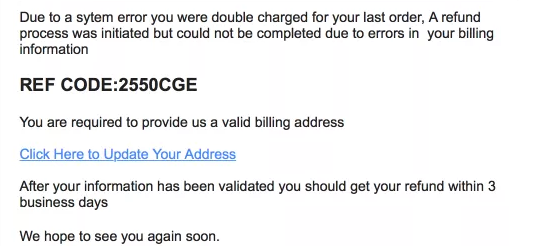
Getting an unexpected windfall of cash? Who wouldn’t want that? Be careful, though: If someone sends you an email saying that you’re due a refund or cash prize of some sort, it’s usually a scam.
You might receive an email that looks like it comes from the local government. The headline will say that you are owed a refund from the agency and that you can claim it online. The body of the message will usually state that the government made an error in calculating your tax bill, and now owes you money, maybe hundreds of dollars.
When you click on the link included in the email to claim the alleged refund, you’ll either run into a spoof site designed to trick you into giving up personal and financial information or your computer or device could be exposed to malware.
How can you tell it’s fake?
There are clues to alert you that this message is fake. The biggest, though, is the message itself. The government will never email you to ask for your personal information. If you get a message saying that they owe you money, call the government agency yourself to check. The odds are highly likely that the government doesn’t owe you anything and that a scammer sent you the message.
Phishing email example: Streaming service phishing scam

You never want your streaming service account to go down. But don’t worry about that email claiming your account is on hold. It’s not true.
The streaming service account-on-hold scam is a popular one, probably because so many of us rely so heavily on these services for entertainment today. In this scam, criminals send an email (supposedly from that streaming service), complete with the company’s logo, saying that the company is having trouble with your current billing information. You’re then asked to click on a link to update your payment method.
You know the rest: The link is a spoof site. When you enter your credit card information, you’re sending it directly to cybercriminals.
How can you tell it’s fake?
Again, the streaming service company won’t reach out to you through email to request your personal information. If you receive a message like this from them, call the company directly to determine if you really do need to update your account.
Also, pay attention to the language of emails like this. In this example, the scammers behind the email start their message with the salutation, "Hi Dear." A business would not address its customers in that way.
Phishing Emails: How to recognize and avoid a Phishing Email
Spotting a phishing email comes down to pointing out anything inconsistent or unusual.
Sometimes it's difficult to recognize what's genuine and what's a phishing attempt. First, you’ll want to be sure that you slow down before opening any links, attachments, or sending a reply.
Here’s an example of how you should react, if you receive a suspect email:
You receive an email politely requesting a donation for victims of the most recent hurricane to make landfall. The sender's domain reads "help@ushurricanesurvivors.net" and though the organization could be legitimate, you haven't heard of it.
Usually, your spam folder shields you from these kinds of emails, but for some reason this one is sitting at the top of your inbox.
You are computer savvy, and you're not taking chances with any email from an organization that's asking for personal and financial information. This is especially true when you didn't request it and can't verify its identity.
By taking a pause, instead of taking immediate action, you’ve taken an important step to protect yourself. However, you’ve still got to determine if this is legitimate or a scam.
Now you need to know exactly what to look for in a phishing email to make a decision.
What does a Phishing Email look like?
One of the reasons phishing emails are so sinister — and unfortunately often successful — is that they're crafted to look legitimate. Generally, the following features are common among phishing emails and should raise red flags:
- Attachments or links.
- Spelling errors.
- Poor grammar.
- Unprofessional graphics.
- Unnecessary urgency about verifying your email address or other personal information immediately.
- Generic greetings like "Dear Customer" instead of your name.
Scammers often rush to get phishing sites up, so some of them will look significantly different from the original company. You can use these traits to pick a malicious email out of your inbox.
Still, it's not always clear what steps to take when you receive a phishing email that has managed to avoid your spam folder.
Tips for handling known Phishing Emails
Being vigilant about spotting phishing emails is key. If you've come across one in your inbox (that hasn’t been auto filtered into spam), use these strategies to avoid becoming a victim of a phishing attack.
- Delete the email without opening it. Most viruses activate when you open an attachment or click a link within an email. But some email clients allow scripting, which makes it possible to get a virus simply by opening a suspicious-looking email. Making it best to avoid opening them all together.
- Manually block the sender. If your email client allows you to manually create a block, you should do so. Make a note of the sender's email domain, and then add the sender to a blocked list. This is especially smart and helpful if you share the email box with anyone in your family. Someone else might stumble upon a legitimate-looking email that isn't part of your spam folder and do something they shouldn't.
- Purchase an extra line of security. You can never be too safe. Consider purchasing antivirus software, to help monitor your email box.
Just remember, the best way to handle a phishing email is to block or delete it immediately. Whether you take any additional actions to limit your exposure to these attacks is a bonus.
Beyond spotting the email and removing it, you can guard yourself with a few extra tips.
Phishing prevention tips
Whether we like it or expect it, you will be the target of these phishing emails every day.
Most of these are filtered out automatically by email providers, and for the most part, users have gotten relatively good at identifying these types of emails and using common sense to not comply with their requests.
But you’ve already seen how deceptive phishing can be. You also know phishing attacks extend into all types of communication and internet browsing — not just emails.
By following a few simple phishing prevention tips, you can greatly reduce your chances of falling victim to a scammer.
Steps to protect yourself from Phishing
Internet protection starts with your mindset and behavior toward potential cyberthreats.
Phishing tricks victims into giving over credentials for all sorts of sensitive accounts, such as email, corporate intranets and more.
Even for cautious users, it's sometimes difficult to detect a phishing attack. These attacks become more sophisticated over time, and scammers find ways to tailor their scams and give very convincing messages, which can easily trip people up.
Here are a few basic measures to always take with your emails and other communications:
1. Employ common sense before handing over sensitive information. When you get an alert from your bank or other major institution, never click the link in the email. Instead, open your browser window and type the address directly into the URL field so you can make sure the site is real.
2. Never trust alarming messages. Most reputable companies will not request personally identifiable information or account details, via email. This includes your bank, insurance company, and any company you do business with. If you ever receive an email asking for any type of account information, immediately delete it and then call the company to confirm that your account is OK.
3. Do not open attachments in these suspicious or strange emails — especially Word, Excel, PowerPoint or PDF attachments.
4. Avoid clicking embedded links in emails at all times, because these can be seeded with malware. Be cautious when receiving messages from vendors or third parties; never click on embedded URLs in the original message. Instead, visit the site directly by typing in the correct URL address to verify the request, and review the vendor's contact policies and procedures for requesting information.
5. Keep your software and operating system up to date. Windows OS products are often targets of phishing and other malicious attacks, so be sure you're secure and up to date. Especially for those still running anything older than Windows 10.
Reducing your spam to avoid Phishing
Here are some more useful tips to help you reduce the amount of spam email you receive:
Set up a private email address. This should only be used for personal correspondence. Because spammers build lists of possible email addresses – by using combinations of obvious names, words and numbers – you should try to make this address difficult for a spammer to guess. Your private address should not simply be your first and last name – and you should protect the address by doing the following:
- Never publish your private email address on publicly accessible online resources.
- If you must publish your private address electronically, try to mask it – in order to avoid having the address picked up by spammers. For example, ‘Joe.Smith@yahoo.com’ is an easy address for spammers to find. Try writing it as ‘Joe-dot-Smith-at-yahoo.com’ instead.
- If your private address is discovered by spammers – you should change it. Although this may be inconvenient, changing your email address will help you to avoid spam and scammers.
Set up a public email address. Use this address when you need to register on public forums and in chat rooms, or to subscribe to mailing lists and other Internet services. The following tips will also help you to reduce the volume of spam you receive via your public email address:
- Treat your public address as a temporary address. The chances are high that spammers will rapidly get hold of your public address, especially if it is frequently being used on the Internet.
- Don't be afraid to change your public email address often.
- Consider using a number of public addresses. That way you’ll have a better chance of tracing which services may be selling your address to spammers.
Never respond to any spam. Most spammers verify receipt and log responses. The more you respond, the more spam you’re likely to receive.
Think before you click ‘unsubscribe.’ Spammers send fake unsubscribe letters, in an attempt to collect active email addresses. If you click 'unsubscribe' in one of these letters, it may simply increase the amount of spam you receive. Do not click on 'unsubscribe' links in emails that come from unknown sources.
Keep your browser updated. Make sure that you use the latest version of your web browser and that all the latest Internet security patches have been applied.
Use anti-spam filters. Only open email accounts with providers that include spam filtering. Choose an antivirus and Internet security solution that also includes advanced anti-spam features.
Be careful when you use public Wi-Fi
Public Wi-Fi is convenient when you're not at home or at work, but it provides many different ways for attackers to gain access to your information. You can reduce your risks by taking steps to protect yourself and your data.
Verify hotspot names
An attacker can create their own unencrypted Wi-Fi hotspot whose name is similar to a reputable one in the same area, such as the network in a coffee shop. If you connect to the phishing hotspot, then the attacker can direct you to their own page where you can be exposed to malware or asked to enter private information.
Before you connect to a hotspot, make sure that the hotspot that you plan to use is legitimate. If you can't see the hotspot name posted in an obvious place, then ask an employee at that location.
Deactivate access points to your device
Even if you have connected to a legitimate public Wi-Fi hotspot, then you can still be at risk by being on the same network as an attacker. Public Wi-Fi networks are much less secure than private networks like the one at your home or office.
Protect yourself by turning off file sharing within your network and by activating your firewall before connecting. Even with these precautions, it's still not a good idea to send or receive any sensitive content using a public Wi-Fi network.
Only send and receive sensitive data over a VPN
A virtual private network establishes a secure connection between your device and the VPN company's servers. From there, the VPN servers relay your information to the internet. If an attacker gains access to the data that you are transmitting and receiving through a public Wi-Fi hotspot, then the data is encrypted and not useful to them.
Techradar and PC Mag are good places to start if you want to learn how to choose a VPN.
Without a VPN, the most secure option is to avoid transmitting sensitive information over public Wi-Fi.
Phishing vs the importance of Internet security software
One of the simplest ways to protect yourself from becoming a victim of a phishing scheme is to install and use proper Internet security software on your computer. Internet security software is vital for any user because it provides multiple layers of protection in one simple-to-manage suite.
For the most reliable protection, your security plan should include the following:
Anti-spam software is designed to protect your email account from phishing and junk emails. Aside from working with pre-defined denylists created by security researchers, anti-spam software has intelligence capabilities to learn, over time, which items are junk and which are not. So while you still should be vigilant, you'll get some comfort from knowing that the software is also filtering out potential trouble. Use anti-phishing protection and anti-spam software to protect yourself when malicious messages slip through to your computer.
Anti-malware is included to prevent other types of threats. Similar to anti-spam software, anti-malware software is programmed by security researchers to spot even the stealthiest malware. With ongoing updates from vendors, the software continues to become more intelligent and better able to deal with the latest threats. By using an anti-malware package, you can protect yourself from viruses, Trojans, worms and more.
By combining a firewall, anti-spam and anti-malware into one package, you can provide extra backups that keep your system from being compromised, if you accidentally click on a dangerous link. They are a vital tool to have installed on all your computers as they are designed to complement common sense.
While technology is a rapidly evolving field, by using a security package from a reputable security vendor, you can secure your devices from phishing and other malware threats.
Password management made easy
In addition to having virus protection software on your computer, it is crucial to use a password manager to manage your online credentials.
Today, it is vital to have different passwords for all websites. If a data breach ever occurs, malicious attackers will try using the discovered credentials across the web.
One of the best features of password managers is that they usually automatically fill in login forms to minimize clicking around. Additionally, many password managers include portable editions that can be saved to a USB drive, ensuring that you can take your passwords wherever you go.
While phishing can be a difficult area to tackle at times, by following the simple tips and advice outlined in this article (and embracing proper phishing prevention tools) — you can greatly minimize your risk of falling victim to digital scammers.
What to do?
Follow government guidelines if your personal information is compromised
Personally identifiable information (PII) consists of data that could be used to identify a particular person, or even impersonate them. PII includes the following types of information:
- full name
- email address
- street address
- telephone number
- credit card number
- national identity number, such as SIN, SSN, or passport
- driver's license
- date of birth
If you provided personally identifiable information through a suspicious channel, or your
Shoplazza account was compromised, then refer to guides from your government, such as this information from the Canadian and United States governments below.
Hong Kong
What to do:
File a report:
Canada
What to do:
File a report:
United States
What to do:
File a report:


Comments
Please sign in to leave a comment.